PowaScripts Update: Kerberos Pre-authentication
After reading harmj0y blog post about “Roasting AS-REPs”, I have decided to update the Dump-User.ps1 script in order for it to report on users that don’t have Kerberos pre-authentication enabled. Running the updated version against a “in the wild” target yielded interesting results to say the least.
While I can’t post the results from the “in the wild” domain, I can say that one domain administrator account was vulnerable and it was possible to successfully retrieve the hash for cracking using harmj0y script.
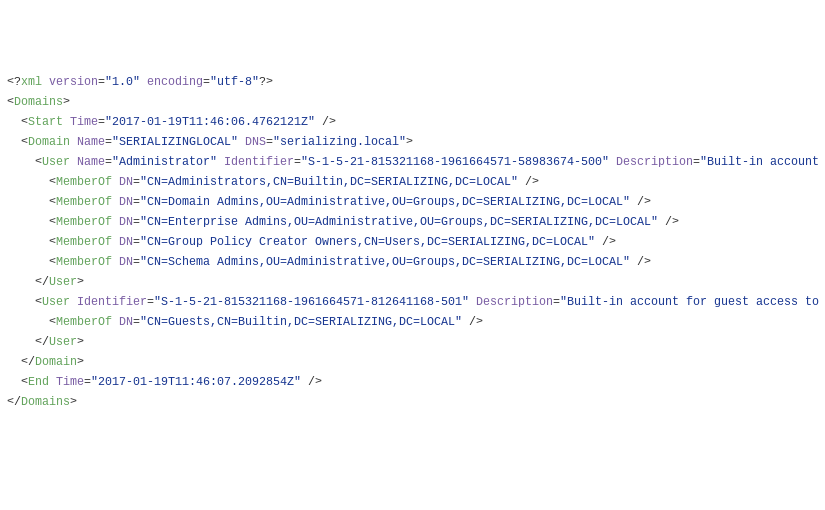
In any case, follows an example result file from my test environment where I have disabled the Kerberos pre-authentication for the domain administrator.
1<?xml version="1.0" encoding="utf-8"?>
2<Domains>
3 <Start Time="2017-01-19T11:46:06.4762121Z" />
4 <Domain Name="SERIALIZINGLOCAL" DNS="serializing.local">
5 <User Name="Administrator" Identifier="S-1-5-21-815321168-1961664571-58983674-500" Description="Built-in account for administering the computer/domain" DN="CN=Administrator,OU=Domain Administration,OU=Users,DC=SERIALIZING,DC=LOCAL" Locked="False" Disabled="False" NoPasswordRequired="False" CanChangePassword="True" PasswordDoesntExpire="True" ExpiredPassword="False" PreAuthNotRequired="True" Created="2016-10-02T12:07:28.0000000Z" Changed="2016-09-02T14:09:58.0000000Z">
6 <MemberOf DN="CN=Administrators,CN=Builtin,DC=SERIALIZING,DC=LOCAL" />
7 <MemberOf DN="CN=Domain Admins,OU=Administrative,OU=Groups,DC=SERIALIZING,DC=LOCAL" />
8 <MemberOf DN="CN=Enterprise Admins,OU=Administrative,OU=Groups,DC=SERIALIZING,DC=LOCAL" />
9 <MemberOf DN="CN=Group Policy Creator Owners,CN=Users,DC=SERIALIZING,DC=LOCAL" />
10 <MemberOf DN="CN=Schema Admins,OU=Administrative,OU=Groups,DC=SERIALIZING,DC=LOCAL" />
11 </User>
12 <User Identifier="S-1-5-21-815321168-1961664571-812641168-501" Description="Built-in account for guest access to the computer/domain" DN="CN=Guest,CN=Users,DC=SERIALIZING,DC=LOCAL" Locked="False" Disabled="True" NoPasswordRequired="True" CanChangePassword="True" PasswordDoesntExpire="True" ExpiredPassword="False" Created="2016-10-02T12:07:28.0000000Z" Changed="2016-09-02T12:52:13.0000000Z">
13 <MemberOf DN="CN=Guests,CN=Builtin,DC=SERIALIZING,DC=LOCAL" />
14 </User>
15 </Domain>
16 <End Time="2017-01-19T11:46:07.2092854Z" />
17</Domains>
The scripts can be found in the project page. Cheers ;)
Categories
Tags
active-directory
acunetix-wvs
android
applocker
aruba-networks
attck
banking
bios
brute-force
bugcrowd
cac-ipc
cheat
cisco-anyconnect
code-injection
csharp
cuckoo-sandbox
e-gpu
emofishes
emotions
fireeye
gpo-bypass
group-policy-objects
honeypot
hook-functions
hp
hpqpswdd
hugo
ivre
lemp
metasploit
paranoid-fish
passwords
portuguese
powascripts
powershell
qemu
raspberry-pi
razer
red-team
soho
ssh
suricata
technicolor
titan-quest
tls
tq-invincible
usb
virtualbox
volatility
wordpress
yara