Posts Tagged With "Active Directory"
Bypass All The GPOs
During a red team engagement, one has landed on a machine with the need to make an application “ignore” Group Policies enforced configurations. This application runs on the context of the user but the settings are only changeable with administrative privileges and without access to a highly privileged account how can one make the application ignore these settings?
Read More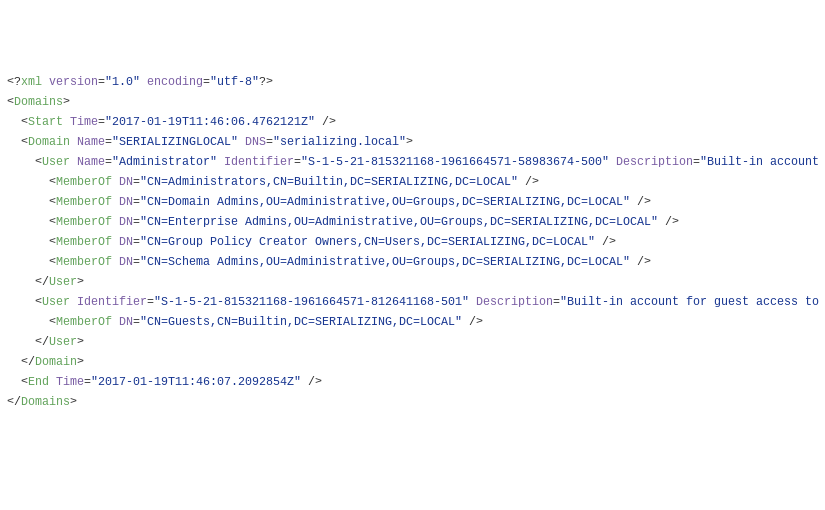
PowaScripts Update: Kerberos Pre-authentication
After reading harmj0y blog post about “Roasting AS-REPs”, I have decided to update the Dump-User.ps1 script in order for it to report on users that don’t have Kerberos pre-authentication enabled. Running the updated version against a “in the wild” target yielded interesting results to say the least.
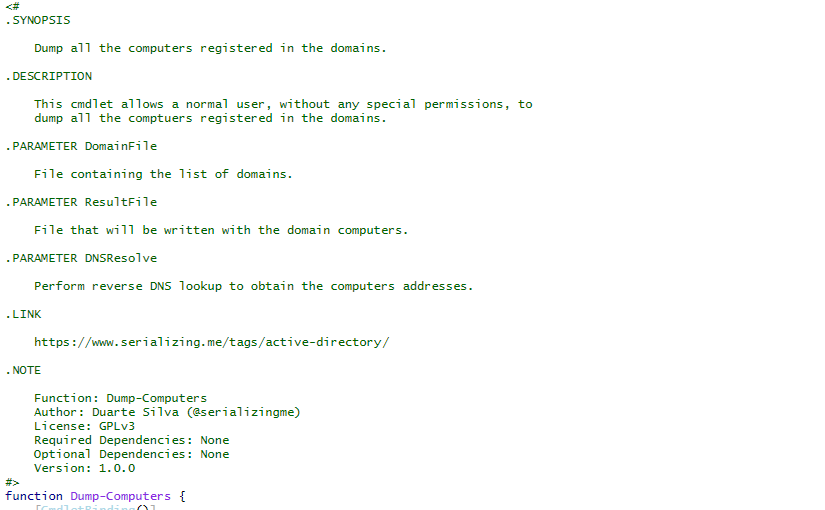
Active Directory Dump
During many penetration tests (or red versus blue team exercises), I have found myself with the need to investigate users, groups, computers and policies of a Windows domain. To do that, I have developed a series of PowerShell scripts that dump all that information from Active Directory into XML files.
Read More