Posts Archived Under "Incident Response"
Inspecting AppLocker Policy
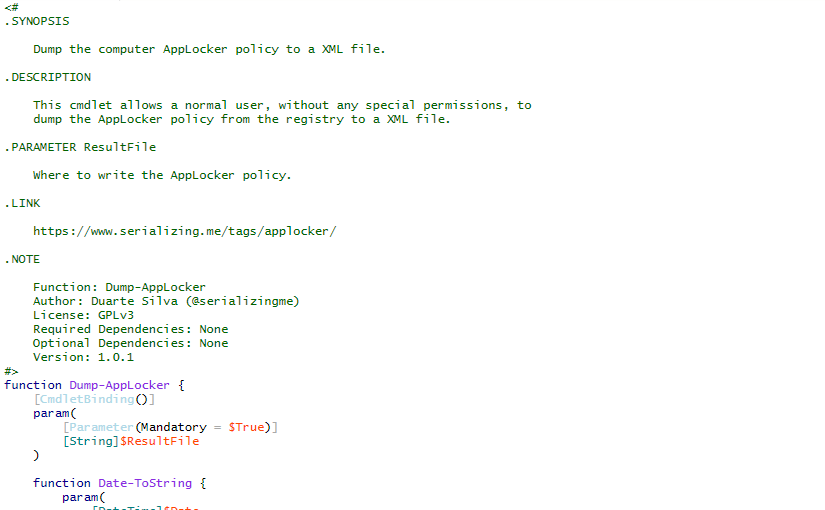
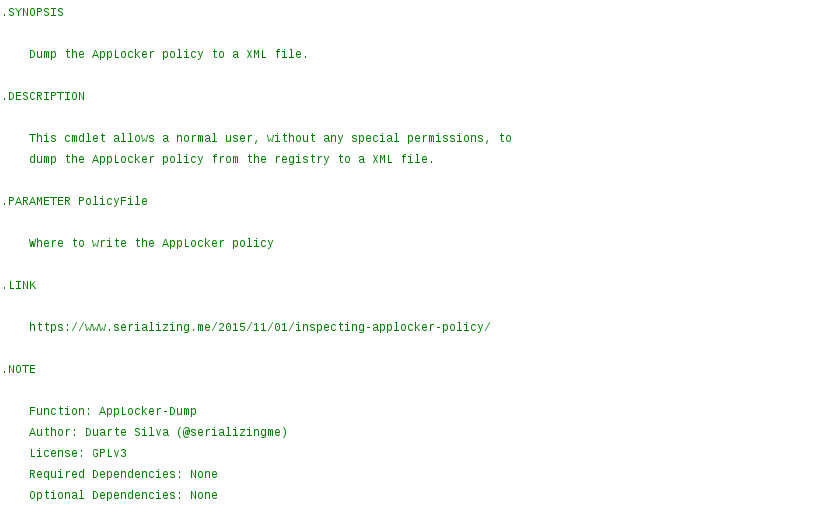
While doing incident response, if AppLocker is being used but the computer still got infected by a malicious executable, it is useful to know exactly what AppLocker policy is currently applied.
Read More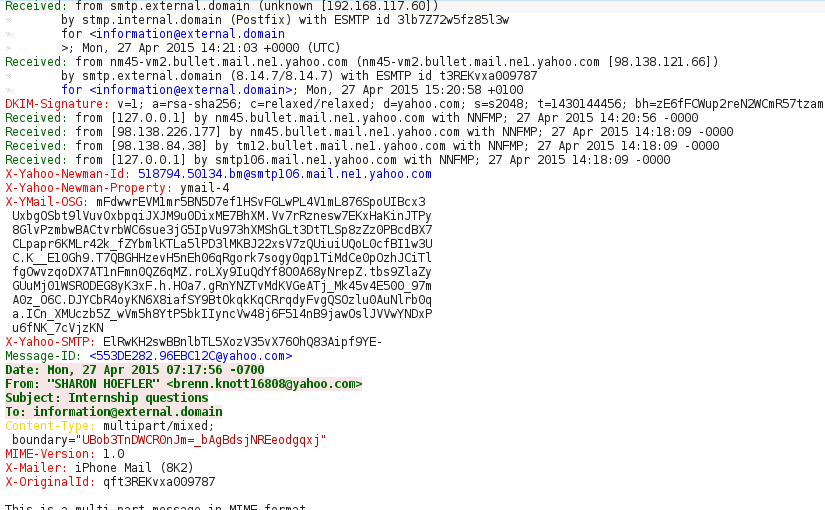
"Check my CV", Generating YARA Rules
Recently, one e-Mail that was sent to one of my colleagues caught my attention. The message was quite believable but there were some little subtleties that gave it away. First step was to get the attachment out of the message and do an initial analysis.
Read MoreCategories
Tags
active-directory
acunetix-wvs
android
applocker
aruba-networks
attck
banking
bios
brute-force
bugcrowd
cac-ipc
cheat
cisco-anyconnect
code-injection
csharp
cuckoo-sandbox
e-gpu
emofishes
emotions
fireeye
gpo-bypass
group-policy-objects
honeypot
hook-functions
hp
hpqpswdd
hugo
ivre
lemp
metasploit
paranoid-fish
passwords
portuguese
powascripts
powershell
qemu
raspberry-pi
razer
red-team
soho
ssh
suricata
technicolor
titan-quest
tls
tq-invincible
usb
virtualbox
volatility
wordpress
yara