Posts
Titan Quest Invincibility Cheat
In the last level of Titan Quest, every player will have to face the titan Typhon, Bane of the Gods. A task that is very far from easy…
Read More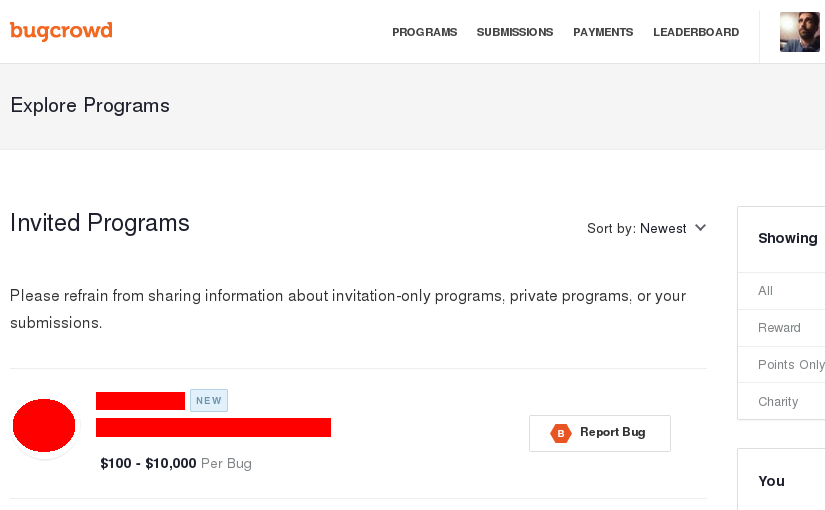
Bug Bounty, Serious Rewards
My first Bugcrowd private bug bounty program that involves some serious rewards. One thing is for sure, they got my attention :D
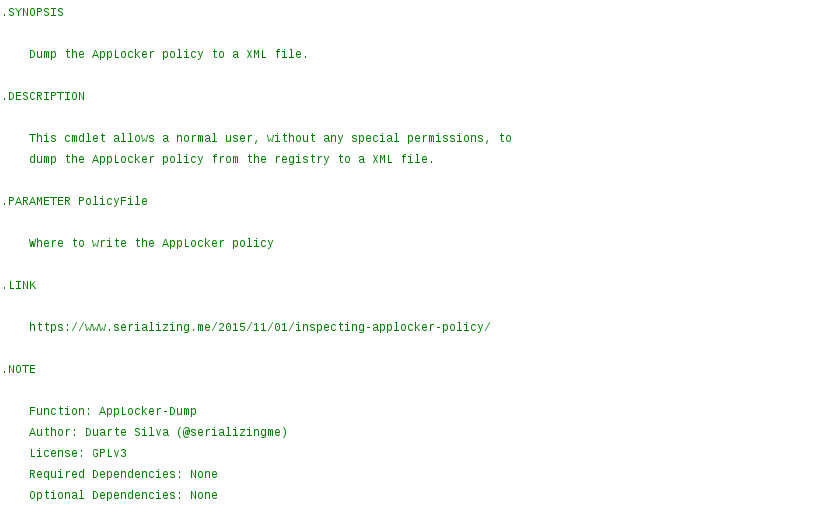
Inspecting AppLocker Policy
While doing incident response, if AppLocker is being used but the computer still got infected by a malicious executable, it is useful to know exactly what AppLocker policy is currently applied.
Read More
Reversing Aruba Instant Firmware
Aruba produces two different software loads for their Access Point hardware. The first is called ArubaOS and the second is called Aruba Instant. With ArubaOS, the AP requires a Mobility Controller (hardware) to be installed in the network. With the Aruba Instant it is possible to run AP’s independently (standalone mode) or in a cluster, with no Mobility Controller in the network.
What follows is the full process to extract all the files recreating the Aruba Instant firmware file system.
Read More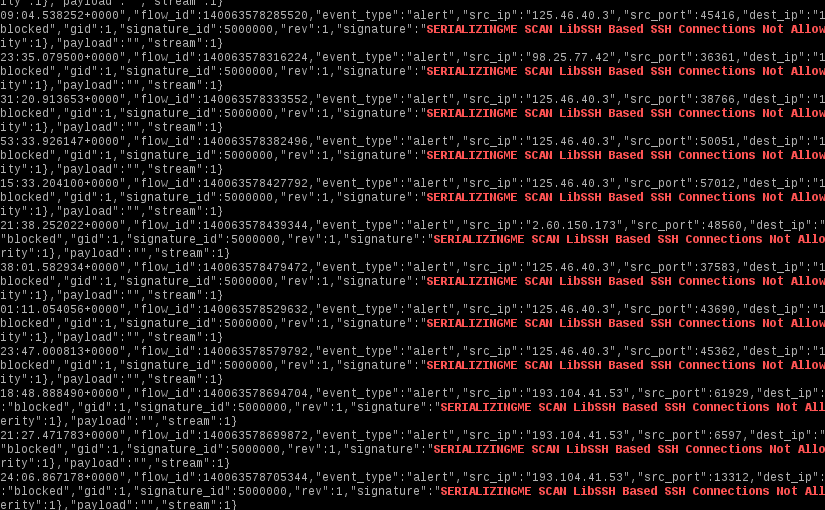
SSH Brute Force and Suricata
Since SSH is one of the most pervasive ways to manage servers remotely, it is also one of the most plagued by brute force attacks. What follows is a simple set of Suricata rules to stop the majority of SSH brute force attacks. It will drop connections based on the reported SSH client version.
Read More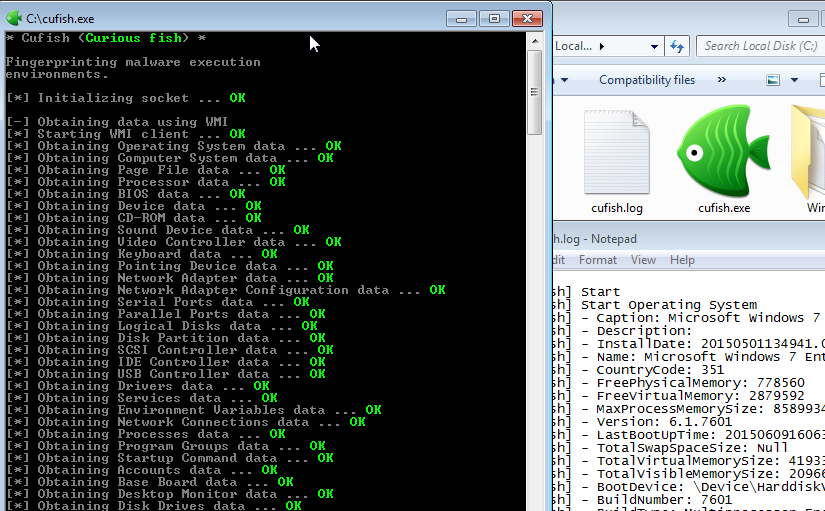
Curious Fish is Curious
Testing virtualized malware sandboxes with Paranoid Fish wasn’t enough, there might be other things that could be improved to avoid malware detection. Enter Curious Fish, a tool to help fingerprinting sandboxes.
Read More
Portuguese Banking Apps, Yay or Nay?
I have been using my bank mobile application for a while, but never had a look at its security. This is an account of my findings, not only on that specific application, but on eight of the offerings available in the Portuguese market.
Read More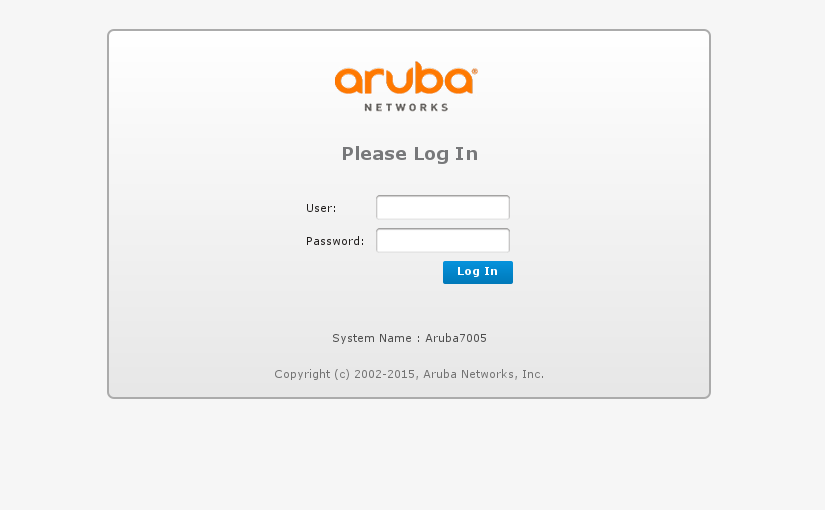
Reversing ArubaOS Firmware
Some time ago, I had the chance to get my hands on a ArubaOS firmware, what follows is the full process to extract all the files recreating the appliance running file system. This had the objective of fuzzing the extracted binaries in QEMU (ArubaOS management console is CGI based).
Read More